- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Re: DoS Attacks in the logs
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
DoS Attacks in the logs
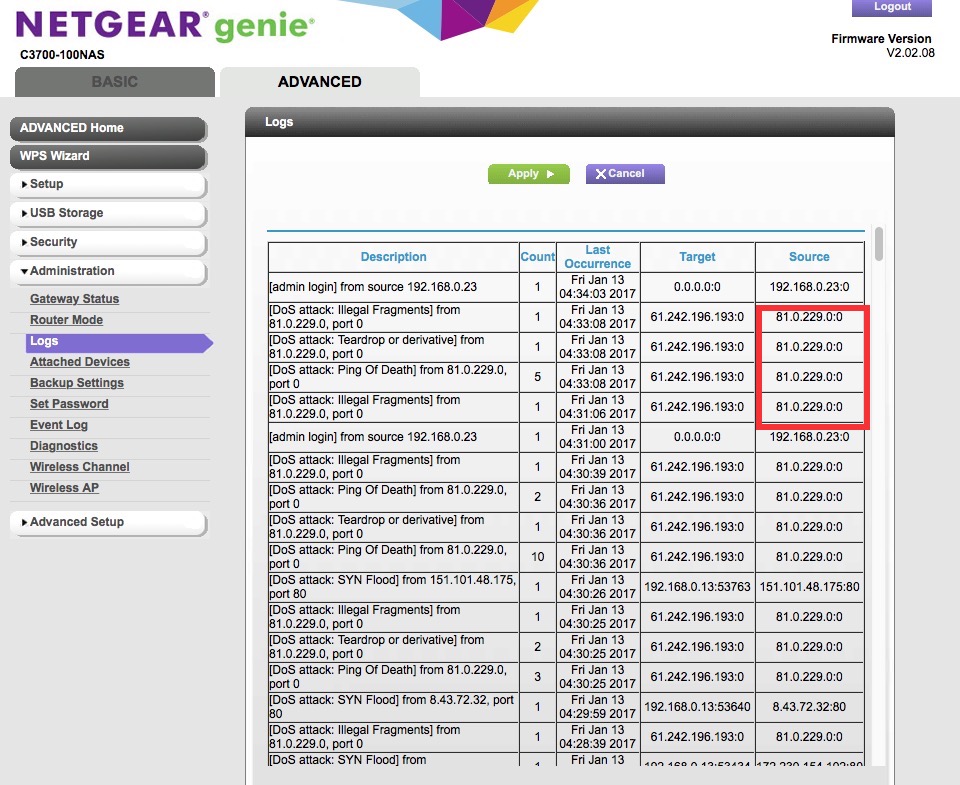
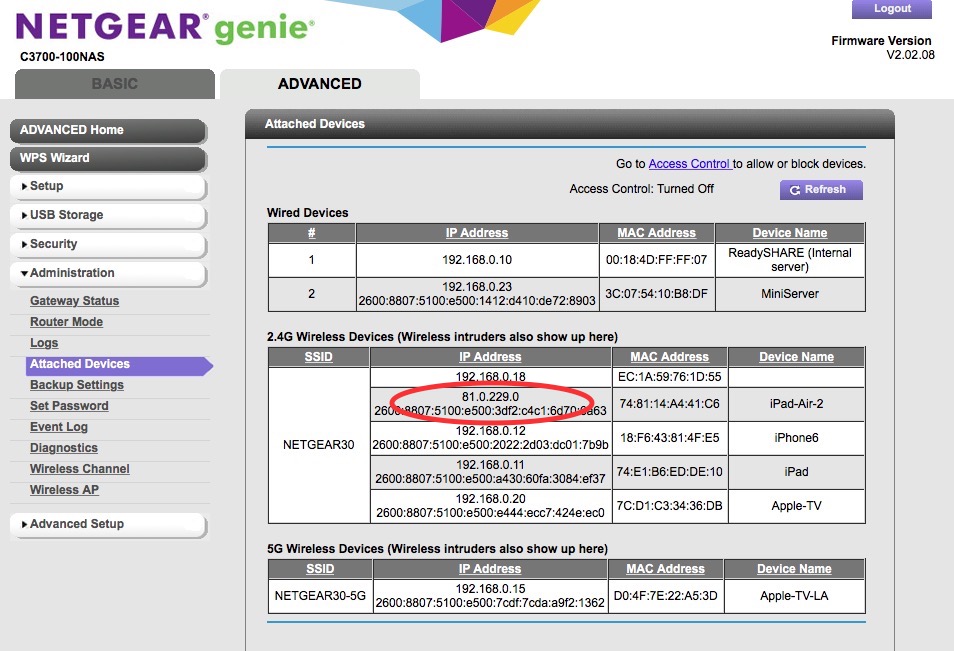
I have been getting disconnected from the internet at different times over the past week. At first i thought it might have been an ISP issue, spoke to them and multiple line checks revealed no issues....during the drop outs i wasnt able to ping the router (Nighthawk D7000) or any devices on my home network, i have checked the logs and it contained multiple DoS attack entries as below
DoS attack: ACK Scan] from source: 51.254.7.95:80 Sunday, March 05,2017 08:43:45
[DoS attack: ACK Scan] from source: 51.254.7.95:80 Sunday, March 05,2017 08:42:30
[DoS attack: ACK Scan] from source: 51.254.7.95:80 Sunday, March 05,2017 08:41:14
[DoS attack: ACK Scan] from source: 51.254.7.95:80 Sunday, March 05,2017 08:39:59
I went ahead and disabled remote management and turned off upnp etc....propblem still persisted. I have changed the router to a new one (same model) and Dos attacks continued. With our ISP i get a new public IP address everytime i restart my router so there is really mo chance of this being a Real DoS attack as my IP changed on a daily basis (atleast over the past week)
Done a scan on all the home laptops for any malware nothing!!
I am stuck and not sure what to do? Is this a fault with the firmware / netgear equipments?
Any help is greatly appreciated
Cheers
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Im also having the same problems as you. Its constant, Ive been trying to find a way to block this IP address but with no luck. I lose connection each time this happens.
| Teardrop or derivative] | 1 | Sun Mar 05 17:56:37 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Illegal Fragments] | 1 | Sun Mar 05 17:56:37 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Ping Of Death] | 3 | Sun Mar 05 17:56:37 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Illegal Fragments] | 1 | Sun Mar 05 17:56:40 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Ping Of Death] | 1 | Sun Mar 05 17:56:40 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 2 | Sun Mar 05 17:56:42 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Illegal Fragments] | 2 | Sun Mar 05 17:56:46 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 1 | Sun Mar 05 17:56:48 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Ping Of Death] | 1 | Sun Mar 05 17:56:50 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 1 | Sun Mar 05 17:56:55 2017 | 209.251.223.129:0 | 73.0.209.0:0 |
| [Illegal Fragments] | 2 | Sun Mar 05 17:56:55 2017 | 209.251.223.129:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 4 | Sun Mar 05 17:57:59 2017 | 209.251.223.129:0 | 73.0.209.0:0 |
| [Ping Of Death] | 1 | Sun Mar 05 18:01:04 2017 | 209.251.223.129:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 1 | Sun Mar 05 18:02:24 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Illegal Fragments] | 1 | Sun Mar 05 18:02:25 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Ping Of Death] | 1 | Sun Mar 05 18:02:25 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 1 | Sun Mar 05 18:02:25 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Ping Of Death] | 2 | Sun Mar 05 18:02:35 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 1 | Sun Mar 05 18:02:52 2017 | 209.251.223.129:0 | 73.0.209.0:0 |
| [TCP- or UDP-based Port Scan] | 1 | Sun Mar 05 18:07:13 2017 | ||
| [Ping Of Death] | 2 | Sun Mar 05 18:07:15 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 2 | Sun Mar 05 18:07:18 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Ping Of Death] | 1 | Sun Mar 05 18:07:24 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 1 | Sun Mar 05 18:07:27 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Ping Of Death] | 2 | Sun Mar 05 18:07:28 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Teardrop or derivative] | 2 | Sun Mar 05 18:07:30 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [Illegal Fragments] | 1 | Sun Mar 05 18:11:02 2017 | 121.13.197.171:0 | 73.0.209.0:0 |
| [TCP- or UDP-based Port Scan] | 1 | Sun Mar 05 18:16:51 2017 | ||
| [FAILURE: User interface login] | 2 | Sun Mar 05 18:16:56 2017 | ||
| [SUCCESS: User interface login] | 1 | Sun Mar 05 18:17:00 2017 |
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
I am having the same issue with these attacks. I am at my wit's end with what to do. I work from home and cannot afford to keep having these dropped internet issues. The attacks are happening daily, multiple times a day. Is there anything that can help? I am so freaking aggravated, it isn't funny. These are but just a few of the attacks. My provider is Cox Communications.
| DoS attack] ICMP Flood from 206.117.25.90 | 1 | Monday, 06 Mar 2017 09:48:06 | 68.102.73.127 | 206.117.25.90 |
| [DoS attack] ICMP Flood from 129.82.138.44 | 1 | Monday, 06 Mar 2017 07:56:30 | 68.102.73.127 | 129.82.138.44 |
| [DoS attack] ICMP Flood from 212.1.84.56 | 1 | Monday, 06 Mar 2017 07:24:23 | 68.102.73.127 | 212.1.84.56 |
| [DoS attack] ICMP Flood from 195.251.255.69 | 1 | Monday, 06 Mar 2017 07:00:58 | 68.102.73.127 | 195.251.255.69 |
| [DoS attack] AIF:Dropped INPUT packet: PROTO:TCP SPT:9090 DPT:22 | 1 | Monday, 06 Mar 2017 05:55:01 | 68.102.73.127 | 221.229.160.210 |
| [DoS attack] ICMP Flood from 203.178.148.19 | 1 | Monday, 06 Mar 2017 05:06:49 | 68.102.73.127 | 203.178.148.19 |
| [DoS attack] ICMP Flood from 187.54.115.129 | 1 | Monday, 06 Mar 2017 05:00:33 | 68.102.73.127 | 187.54.115.129 |
| [DoS attack] ICMP Flood from 185.94.111.1 | 1 | Monday, 06 Mar 2017 04:43:12 | 68.102.73.127 | 185.94.111.1 |
| [DHCP IP: (192.168.0.104)] to MAC address 00:0b:82:67:70:9d | 1 | Monday, 06 Mar 2017 04:32:38 | 0.0.0.0 | 0.0.0.0 |
| [DoS attack] ICMP Flood from 206.117.25.90 | 1 | Monday, 06 Mar 2017 01:33:03 | 68.102.73.127 | 206.117.25.90 |
| [DoS attack] AIF:Dropped INPUT packet: PROTO:TCP SPT:56766 DPT:23 | 1 | Monday, 06 Mar 2017 00:13:49 | 68.102.73.127 | 5.232.188.59 |
| [DoS attack] ICMP Flood from 129.82.138.44 | 1 | Sunday, 05 Mar 2017 23:42:13 | 68.102.73.127 | 129.82.138.44 |
| [DoS attack] ICMP Flood from 195.251.255.69 | 1 | Sunday, 05 Mar 2017 23:08:04 | 68.102.73.127 | 195.251.255.69 |
| [DoS attack] AIF:Dropped INPUT packet: PROTO:TCP SPT:9090 DPT:22 | 1 | Sunday, 05 Mar 2017 22:34:18 | 68.102.73.127 | 221.229.160.210 |
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Hello KClaeys
I checked and here is where your Dos attacks are coming from
https://ant.isi.edu/datasets/about.html
also are you seeing any type of timeouts in your logs?
DarrenM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Hi Darren,
Thanks for the info. I am planning on writing them a scathing letter to get them to stop. I don't think it is all them though. Anyway, I checked the logs and this is the first thing I saw:
| DoS attack] AIF:Dropped INPUT packet: PROTO:TCP SPT:9090 DPT:22 | 1 | Tuesday, 07 Mar 2017 11:17:48 | 68.102.73.127 | 221.229.160.210 |
| [DoS attack] ICMP Flood from 206.117.25.90 | 1 | Tuesday, 07 Mar 2017 09:49:06 | 68.102.73.127 | 206.117.25.90 |
Any ideas on what to do? I am seriously upset because of the dropped internet. This is really killing my paycheck.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Can you post the power levels on the Cable connection page check to see if anything is off. You may also want to check if you have a cable splitter connected to the modem they can cause some issues try plugging straight to the wall. Also have you had your ISP come out and check your lines?
DarrenM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
I don't use a splitter, so I know that itsn't the problem. I'm going to have the cable company come out, even though they all tell me it's on my end. Here are the logs for the power. Please let me know if you see anything odd.
| <tabindex=-1>Downstream Bonded Channels | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| <tabindex=-1>Upstream Bonded Channels | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Hello KClaeys
All the levels look good from what you posted but those could change when you are losing service maybe its a line issue outside it happens alot when neighbors get cable hooked up a tech could mess someone else connection up I guess you will find out when the tech comes.
DarrenM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Do you have any ideas for me and the OP? Thanks!
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
I gave up on Netgear and bought a Motorola, and have not seen the problem in 3 days now.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Hello Mrcarrotlll
Are you able to post your logs and levels of the modem it could give a better Idea of why the disconnects are happening.
DarrenM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
| <tabindex=-1>Downstream Bonded Channels | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| <tabindex=-1>Upstream Bonded Channels | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Hello MrCarrotlll
The power level look fine what about the logs are you seeing any type of timeouts?
DarrenM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Hi Darren,
The cable company came out and ran a new line from the house to the pole, put a new box on the house, we moved the modem, used new cables on everything and I am still having issues. Now I am getting T3 and T4 timesouts. One day the internet was dropping literally every 10 minutes. Of course, Cox tells me it is on my end and they are getting great signals. Interestingly enough, when I contacted that university about not pinging my internet, I haven't had one DoS attack. Here is the log from today when trouble started (again). I am considering getting a modem from Cox and if I still have the same problems with one of THEIR modems, then I guess it is on them.
|
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
Hello KClaeys
It could be a bigger issue away from your homes lines but yea you may want to test another modem to be sure if its on there end or not but typically those T3 and T4 timeouts are.
DarrenM
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: DoS Attacks in the logs
I've had the same problems each person describes above, have set up trouble tickets, gotten your folks and Time Warner on the phone to duke it out, and it continues several weeks past the support period you offer. Quite frankly, I'm done with Netgear. You don't provide real resolution to this issue, as noted time and time again in reviewing this topic in the support community. My DOS attacks come from sites I frequent as well as sites I've never heard of or visited, nor has anyone else in our house visited them. I understand the device's job is to stop DOS attacks, but it sacrifices connection to the internet in doing so. THAT is the problem as I see it, but I'm woefully ignorant about the complicated world of IT. I'm sure it's more complicated, but the outcome is the same - we get booted from the internet and it takes anywhere from 30-45 minutes for the device to restabilize...until the next DOS attack. I hope you find a solution.
• What is the difference between WiFi 6 and WiFi 7?
• Yes! WiFi 7 is backwards compatible with other Wifi devices? Learn more