- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
FVS336GV2 - IPSec VPN issues
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
FVS336GV2 - IPSec VPN issues
Hello,
I'm trying to set up a Site2Site VPN connection with IPSec, but it seems I'm running into some issues. Phase 1 and 2 are completed succesfully, according to the VPN logs, but still there is no network connection. Seems like firewall issue or something, but I cannot find it. I'll specify the details here:
My site:
Hardware: Netgear Prosafe FVS336Gv2
Firmware: 4.3.1.-18
Remote Site:
Hardware: Cisco ASA
Firmware: No idea
VPN Log:
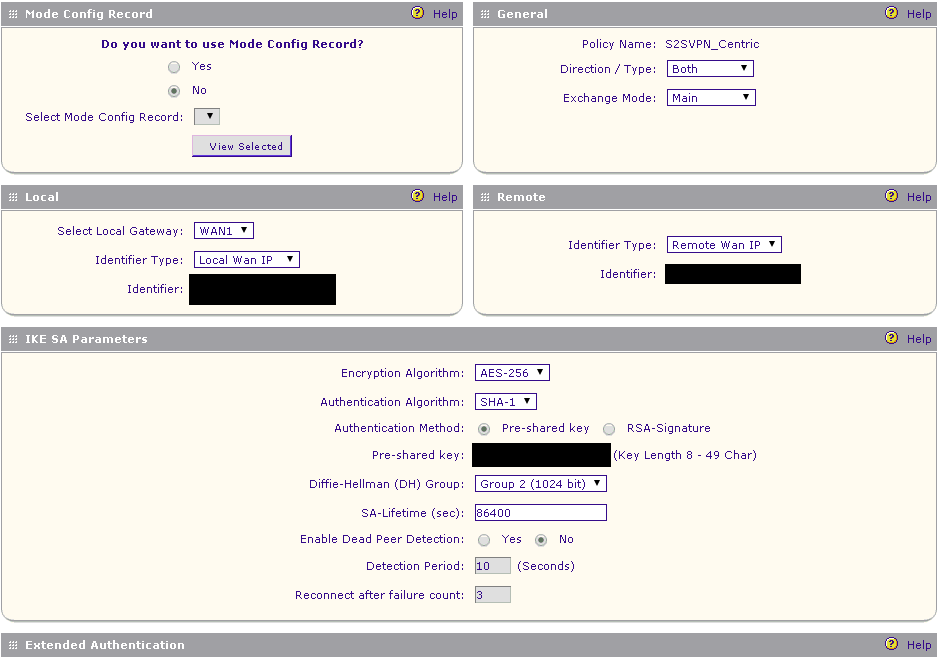
Wed Oct 21 09:21:30 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: Adding IKE configuration with identifier "S2SVPN_Centric"
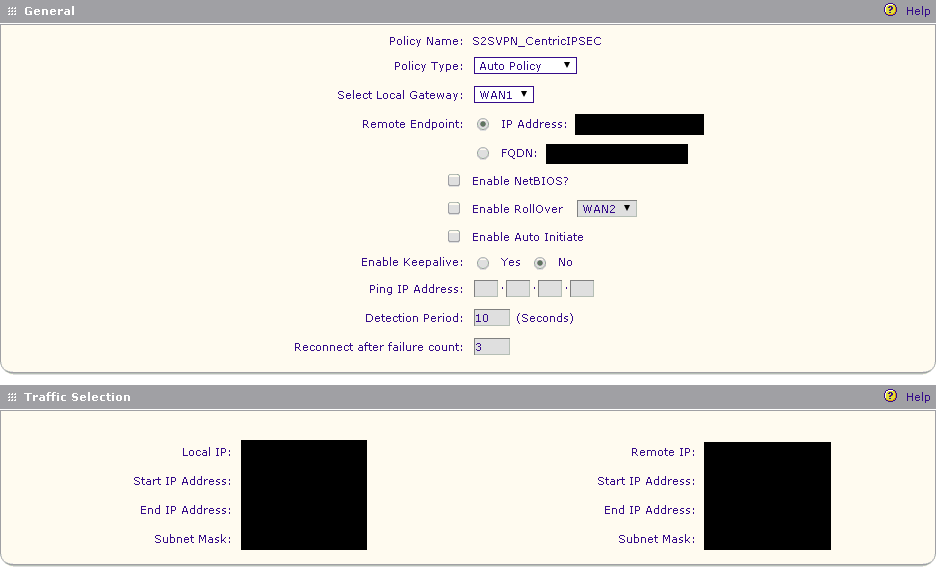
Wed Oct 21 09:21:30 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: Adding IPSec configuration with identifier "S2SVPN_CentricIPSEC"
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: IKE configuration with identifier "S2SVPN_Centric" deleted sucessfully
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: an undead schedule has been deleted: 'purge_remote'.
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: Purged ISAKMP-SA with spi=58dd97e8f0a8f52b:360c6ee035209882.
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] WARNING: no phase2 bounded.
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: Purged ISAKMP-SA with proto_id=ISAKMP and spi=58dd97e8f0a8f52b:360c6ee035209882.
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: IPSec configuration with identifier "S2SVPN_CentricIPSEC" deleted sucessfully
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: an undead schedule has been deleted: 'pk_recvupdate'.
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: purged IPsec-SA proto_id=ESP spi=65796120.
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: purged IPsec-SA proto_id=ESP spi=946730779.
Wed Oct 21 09:21:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: Sending Informational Exchange: delete payload[]
Wed Oct 21 04:48:27 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: [IPSEC_VPN] Purged IPsec-SA with proto_id=ESP and spi=437665354(0x1a163e4a).
Wed Oct 21 04:48:23 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: [IPSEC_VPN] IPsec-SA established: ESP/Tunnel *.*.*.*->*.*.*.* with spi=946730779(0x386df71b)
Wed Oct 21 04:48:23 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: [IPSEC_VPN] IPsec-SA established: ESP/Tunnel *.*.*.*->*.*.*.* with spi=65796120(0x3ebf818)
Wed Oct 21 04:48:23 2015 (GMT +0200): [FVS336Gv2] [IKE] WARNING: attribute has been modified.
Wed Oct 21 04:48:23 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: Initiating new phase 2 negotiation: *.*.*.*[500]<=>*.*.*.*[0]
Wed Oct 21 04:48:23 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: Configuration found for *.*.*.*.
Wed Oct 21 04:48:23 2015 (GMT +0200): [FVS336Gv2] [IKE] INFO: [IPSEC_VPN] IPsec-SA expired: ESP/Tunnel *.*.*.*->*.*.*.* with spi=437665354(0x1a163e4a)
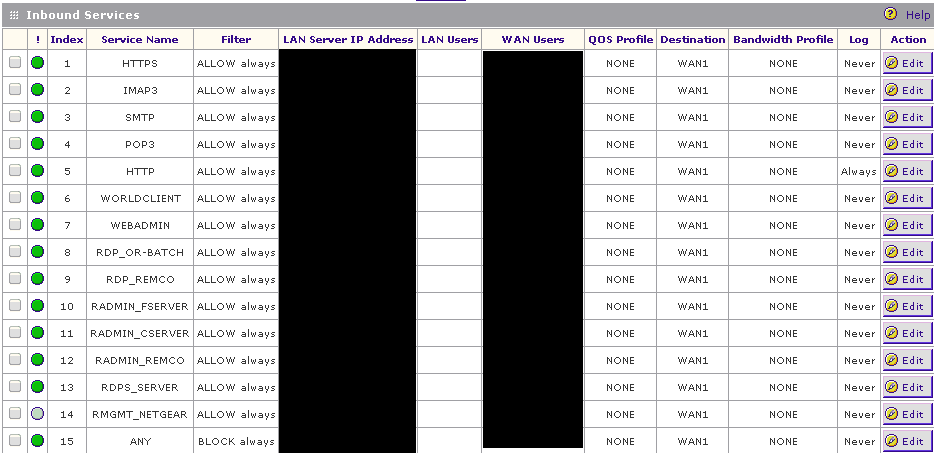
Firewall Rules
Phase 1:
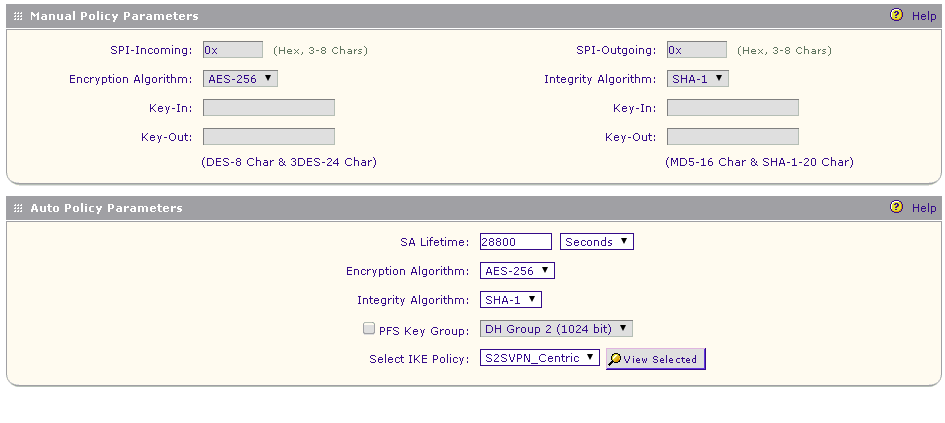
Phase 2 -1:
Phase 2 -2:
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: FVS336GV2 - IPSec VPN issues
Hi ZwaanVOF,
Hope these links I found online might help you as reference guide:
http://vpncasestudy.com/download/pdf/CiscoPIXFirewalltoNegear.pdf
NETGEAR ProSecure UTM to CIsco ASA 5505 VPN Guide
https://www.exadigm.com/GT_IPsec_Setup_Guide_18Dec2012.pdf
Regards,
DaneA
NETGEAR Community Team
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: FVS336GV2 - IPSec VPN issues
Can't read the screenshots.
Delete the Inbound ANY Block Always Rule.
There is no need to mask the private IP's in the screenshots or logs. Without them it's impossible to see where the problem is. Only mask the public IP's partially.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: FVS336GV2 - IPSec VPN issues
You can zoom in and read them. I can also post them again with a large resolution, if that helps you.
The 'Inbound ANY Block Always Rule' is on a certain group of public IP's, not ANY.
The private IP's are a subnet, on both sides. I don't see why the problem should be there..
Problem is still present. I've seen the guides provided by DaneA and shared with the remote site operator, but there's nothing that we already tried. Trial-and-error with the documents is the next step, I think...