- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Re: Some clarity on VLANs needed
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Some clarity on VLANs needed
So I've been struggling for a could of days trying to get a single VLAN setup and this morning I changed the VPID settings and I broke everything.
I read this post from 2017 and I think it will solve my issue.
So my setup is basic. We have a VLAN aware router (Unifi Security Gateway Pro), 4 GS728TP switches, 2012 R2 DHCP server, MyPBX u510 and a bunch of Yealink phones.
Our data LAN has an IP range of 192.168.16.0/24 and the phone system has an IP range of 10.5.5.0/24. Now I understand that the 192.168.16.0/24 range basically runs the default VLAN 1. I have configured the USG-Pro with VLAN 2 for the voice LAN, logged onto all the switches, set VLAN membership on all ports to VLAN 2, I must add that VLAN 1 is untagged on all ports.. Now this is where I need some clarity as at this point I don't have communication between VLAN 1 & VLAN 2. Do I need to set the PVID for all ports to 1?
Some guidance would be greatly appreciated.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Some clarity on VLANs needed
Assuming I understand you right nd you have configured two networks on one port of the USG - what makes VLAN 1 (the "base VLAN") untagged, and the VLAN 2 taged.
You configure a so-called VLAN-trunk, the base LAN 192.168.16.0/24 is VLAN 1 is run [U]ntagged (therfore also PVID 1 - this makes uncoming untagged frames going to VLAN 1, simple!), and the voice VLAN 2 run [T]agged.
If you need a Data access port only, configure it VLAN 1 [U]ntagged, PVID 1 (no other VLAN associations, all empty).
If you need a VoIP access port only, configure it VLAN 2 [U]ntagged, PVID 2 (no other VLAN associations, all empty).
If you need a shared port for Data and VoIP (phone data pass-through), configure it VLAN 1 [U]ntagged, PVID 1 plus VLAN 2 [T]agged.
If the plan is using VoIP and data on one connection (Switch - Phone [1 Gb required typically!] - PC) I owuld suggest using the Netgear switch Auto-VoIP feature, check the phone OID is configured, ... like this you don't have to configure any VLAN tagging on the phone.
This is it. No rocket science. If UniFi is non-transparent what is going on under the sexy user interface - sorry, this is not Netgear's mistake.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Some clarity on VLANs needed
@schumaku wrote:Assuming I understand you right nd you have configured two networks on one port of the USG - what makes VLAN 1 (the "base VLAN") untagged, and the VLAN 2 taged.
You configure a so-called VLAN-trunk, the base LAN 192.168.16.0/24 is VLAN 1 is run [U]ntagged (therfore also PVID 1 - this makes uncoming untagged frames going to VLAN 1, simple!), and the voice VLAN 2 run [T]agged.
If you need a Data access port only, configure it VLAN 1 [U]ntagged, PVID 1 (no other VLAN associations, all empty).
If you need a VoIP access port only, configure it VLAN 2 [U]ntagged, PVID 2 (no other VLAN associations, all empty).
If you need a shared port for Data and VoIP (phone data pass-through), configure it VLAN 1 [U]ntagged, PVID 1 plus VLAN 2 [T]agged.
If the plan is using VoIP and data on one connection (Switch - Phone [1 Gb required typically!] - PC) I owuld suggest using the Netgear switch Auto-VoIP feature, check the phone OID is configured, ... like this you don't have to configure any VLAN tagging on the phone.
This is it. No rocket science. If UniFi is non-transparent what is going on under the sexy user interface - sorry, this is not Netgear's mistake.
Ok, I figured it would be this: If you need a shared port for Data and VoIP (phone data pass-through), configure it VLAN 1 [U]ntagged, PVID 1 plus VLAN 2 [T]agged.
Will give it all a bash and report back, thank you.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Some clarity on VLANs needed
@djmohr wrote:
@schumaku wrote:Assuming I understand you right nd you have configured two networks on one port of the USG - what makes VLAN 1 (the "base VLAN") untagged, and the VLAN 2 taged.
You configure a so-called VLAN-trunk, the base LAN 192.168.16.0/24 is VLAN 1 is run [U]ntagged (therfore also PVID 1 - this makes uncoming untagged frames going to VLAN 1, simple!), and the voice VLAN 2 run [T]agged.
If you need a Data access port only, configure it VLAN 1 [U]ntagged, PVID 1 (no other VLAN associations, all empty).
If you need a VoIP access port only, configure it VLAN 2 [U]ntagged, PVID 2 (no other VLAN associations, all empty).
If you need a shared port for Data and VoIP (phone data pass-through), configure it VLAN 1 [U]ntagged, PVID 1 plus VLAN 2 [T]agged.
If the plan is using VoIP and data on one connection (Switch - Phone [1 Gb required typically!] - PC) I owuld suggest using the Netgear switch Auto-VoIP feature, check the phone OID is configured, ... like this you don't have to configure any VLAN tagging on the phone.
This is it. No rocket science. If UniFi is non-transparent what is going on under the sexy user interface - sorry, this is not Netgear's mistake.
Ok, I figured it would be this: If you need a shared port for Data and VoIP (phone data pass-through), configure it VLAN 1 [U]ntagged, PVID 1 plus VLAN 2 [T]agged.
Will give it all a bash and report back, thank you.
Sadly this didn't work for me.
All ports are tagged with VLAN 2 and PVID is set to 1. I don't seem to be able to ping or connect to any other the voice devices. What's interesting though is that I tried to untag VLAN 2 from all port then I get a single ping reply from the PBX. I've disabled Ingress Filtering as well and this made no difference.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Some clarity on VLANs needed
@djmohr wrote:All ports are tagged with VLAN 2 and PVID is set to 1.
This alone isn't sufficient.
Re-read the above.
For the testing and learning curve, I suggest to configure two access-type ports, one on VLAN 1 [U]ntgged and PVID 1, another with VLAN2 [U]ntagged and PVID 2. This gives you two ports for testing the VLANs to the router...
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Some clarity on VLANs needed
@schumaku wrote:
If you need a shared port for Data and VoIP (phone data pass-through), configure it VLAN 1 [U]ntagged, PVID 1 plus VLAN 2 [T]agged.
Sorry, bit confussed now. Is VLAN 2 supposed to be tagged or untagged, the quoted text suggests that it needs to be tagged.
This alone isn't sufficient.
Re-read the above.
For the testing and learning curve, I suggest to configure two access-type ports, one on VLAN 1 [U]ntgged and PVID 1, another with VLAN2 [U]ntagged and PVID 2. This gives you two ports for testing the VLANs to the router...
The above suggests untag it but set the PVID to 2.
I know from an early mistake that tagging all ports on VLAN 2 and setting PVID to 2 results in loosing connection completely.
Will set as you suggest for testing.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Some clarity on VLANs needed
I should add that I can reach the VLAN configured on the USG-Pro, I get ping replies from 10.5.5.1 which is the router. But the same isn't true for any other device on the 10.5.5.0/24 range.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Some clarity on VLANs needed
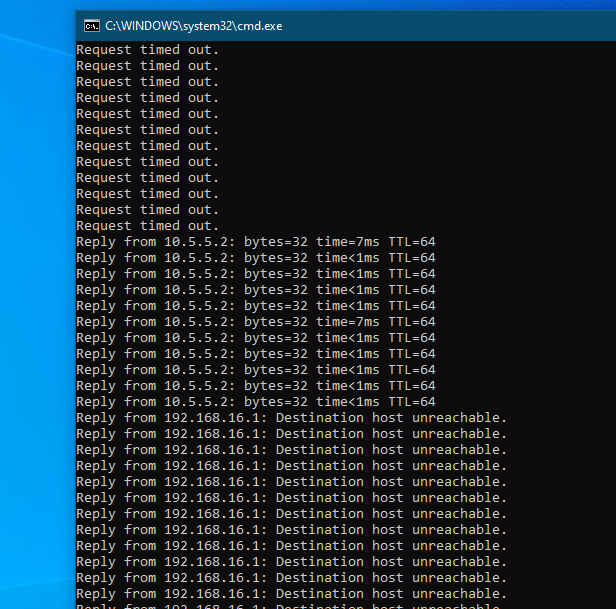
I'm getting strange results when switching between Tagged and Untagged for VLAN.
The above screen happens when I change the ports from Tagged to Untagged for VLAN 2. Switching back to Tagged just results in a Request timed out.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Some clarity on VLANs needed
That's why i had proposed to configure two access ports into each VLAN - this allows to figure out if the VLAN config of the router and the switch VLANs are workable. A test computer plugged to each port must get an IP from the relevant VLAN and iP subnet / DHCP server, and must be able to ping each subnet default gateway.