
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Re: Scam "Firmware Update" email - 12/01/2017
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
On 12/01/17, I received an email titled "Important Security Update from NETGEAR", sent from "<security@e.netgear.com>".
It directed me to visit netgear.com/support to obtain a download of a new firmware version.
Is this a legitimate notification or a scam?
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, you got the RIGHT thing, the ZIP file with 2 files in it:
K:\Inet DL\R7000-V1.0.9.14_1.2.25>dir
Volume in drive K is Disk_K
Volume Serial Number is 0F0B-10C0
Directory of K:\Inet DL\R7000-V1.0.9.14_1.2.25
12/01/2017 03:45 PM <DIR> .
12/01/2017 03:45 PM <DIR> ..
11/08/2017 10:31 PM 30,859,322 R7000-V1.0.9.14_1.2.25.chk
12/01/2017 04:03 AM 2,894 R7000-V1.0.9.14_1.2.25_Release_Notes.html
The reason Windows calls a file with an extension of .chk a "recovered file fragments" is because when CHKDSK finds file problems it creates a file with that extension.
It is ALSO a file extension NetGear uses for it flashes.
All you need do is open the browser to the Router, go to the Advanced tab -> Administration -> Router Update and browse for that .chk file and UPLOAD it.
Alternatively from that same page you could CHECK for a new version, but sometimes it takes a few days after release for that to work and be able to get the new flash for you.
There is no way to click on that file and have it do the update, only the process above.
All Replies
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
Possibly legit? New Firmware was released for the R7000, R7000-V1.0.9.14_1.2.25.chk, and I think it was yesterday that it happened? Not announced here but there is a thread for it.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
Thank you. I would not have thought to question the email except that my attempt to follow the embedded link was blocked by the Malwarebytes security software on my machine as a suspicious site. I will await response from a netgear rep before proceeding.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
I usually will not take a link in an e-mail when I suspect it might be spam or phishing. I enter the location manually, like in this case go to NETGEAR and click on SUPPORT and drill down into the site for downloads for the R7000.
It could very well be suspect e-mail taking advantage that Netgear DID release new firmware. Not sure how someone would know you had an R7000 though other than Netgear (I never got an e-mail about an update, but maybe it was sent out in groups and takes a few days?).
The new flash is available here --> https://www.netgear.com/support/product/r7000.aspx#download
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
Well, that's the thing - the email DID NOT specifically identify the R7000 we own, which made me a bit more suspicious. A non-specific blanket invitation not identifying device model is going to seem sketchy - as though netgear's customer account base may have been hacked for addresses.
It asked that we go to the site and enter our device model number, & etc.
In any event, i independently accessed the download center through my legit netgear account to see what firmware updates were available.
If, as now seems likely, this was a legitimate "update" notification email, it was very poorly handled by netgear. The sender's address itself (security@e.netgear.com - 108.168.157.87) seemed odd and suspicious. In an era of paranoia over malware and bogus communications, this practice doesn't much help customer confidence.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
Not unusual for companies to use a 3rd party to send out 'blast' emails? That site is not known for malware either (https://www.malwares.com/report/ip?ip=108.168.157.87).
You would have also found the new firmware release here (https://community.netgear.com/t5/Nighthawk-WiFi-Routers/New-R7000-Firmware-Version-1-0-9-14-Released...) as well. Not a STICKY yet though.
You also didn't need to sign-in to Netgear to get the flash.
You said "It asked that we go to the site and enter our device model number, & etc." which is correct, but unless the Netgear site had a link or was hijacked you'd be doing the right thing. Since I use different passwords for sites, I can't see any possible 'damage' if someone got my credentials for this site? Worst case, cause havoc in the forums and I'd be locked out I'd think? No money or hardware could be stolen from me? Now if I used common credentials across many sites (and I'm sure some people do) that would be a different issue.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
Yep, the "blast" outfit checks out (it is, as you point out, just a mass-mailing outfit), but I'm now puzzled as to why Malwarebytes blocked the linked site.
Yeah, I didnt really need to formally logon to netgear, but was just trying to be careful - and I never use common credentials across sites.
Thanks again for your help in addressing my concerns! Truly appreciated!
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
@WTMorgan wrote:but I'm now puzzled as to why Malwarebytes blocked the linked site.
Well it could have been a spam site. Don't forget, what you see in an e-mail client as a link isn't always the true link you will go to. You'd have to look either at the status line when the mouse is over the link if your e-mail client has one otherwise the e-mail source to determine if the link shown is the same you would go to.
Also possible it was the first time you went to that particular site (or in the case of the d/l it is NEW and Malware detected it) and Malware was warning you? Hard to say without more details. Malware might also have a log that would add more info why it did that?
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
Well, now I'm in some sort of bizarre loop.
Clicking the "download" link retrieves a zipped package which contains:
The second file is the release notes asnd installation instructions.
The first file is titled "recovered file fragments". Clicking to open it gets me an warning pop-up with option to "search the web for a program" to open it.
Clicking any of the resulting links from that search causes Malwarebytes to block access (with an option to bypass the block).
Well, I don't want to bypass the Malwarebytes block before I understand what is going on.
This (ostensibly) straigtforward firmware update is becoming convoluted.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
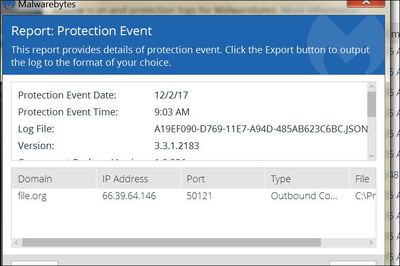
Ah, forgot to mention that the Malwarebytes log entry for the original block provides only the sparcest of details...
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, you got the RIGHT thing, the ZIP file with 2 files in it:
K:\Inet DL\R7000-V1.0.9.14_1.2.25>dir
Volume in drive K is Disk_K
Volume Serial Number is 0F0B-10C0
Directory of K:\Inet DL\R7000-V1.0.9.14_1.2.25
12/01/2017 03:45 PM <DIR> .
12/01/2017 03:45 PM <DIR> ..
11/08/2017 10:31 PM 30,859,322 R7000-V1.0.9.14_1.2.25.chk
12/01/2017 04:03 AM 2,894 R7000-V1.0.9.14_1.2.25_Release_Notes.html
The reason Windows calls a file with an extension of .chk a "recovered file fragments" is because when CHKDSK finds file problems it creates a file with that extension.
It is ALSO a file extension NetGear uses for it flashes.
All you need do is open the browser to the Router, go to the Advanced tab -> Administration -> Router Update and browse for that .chk file and UPLOAD it.
Alternatively from that same page you could CHECK for a new version, but sometimes it takes a few days after release for that to work and be able to get the new flash for you.
There is no way to click on that file and have it do the update, only the process above.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
Thanks again, Irv - ...I brought up the Neatgear Genie app on my phone...checked for firmware updates/logged on to the extender...and took about 1.5 min to do the update with the new firmware version. Bang. Installed. Done.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: Scam "Firmware Update" email - 12/01/2017
I have an R6400 and got the email from "e.netgear..." so no way clicking on any links as that's how I got caught up in a phishing scam from a Kasperski clone years ago. I expect to get a message directly from the application (NetGenie) . And by the way why cannot I open it by clicking on the icon?
• Introducing NETGEAR WiFi 7 Orbi 770 Series and Nighthawk RS300
• What is the difference between WiFi 6 and WiFi 7?
• Yes! WiFi 7 is backwards compatible with other Wifi devices? Learn more

