- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Re: SRX5308 Only two IPSEC Channels working over same IKE
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
SRX5308 Only two IPSEC Channels working over same IKE
Hello,
I have configured two SRX5308 (R1, R2) to connect over a IKE Channel (IKE1). This channel were used by three IP-Sec Channels (IPSEC1 - IPSEC3). All Channels are configured with the same subnet on R1 side and different subnets on R2 side. Anything else are common configured.
As soon as I enabled the IPSec Channels, two channels are up and one not. If I disabled and reenabled the channels, sometimes two other channels up and one not.
Summary I mean: Maximum two random channels are up.
Is the SRX5308 limited to two IPSECs per IKE Channel?
Best regards
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: SRX5308 Only two IPSEC Channels working over same IKE
Hi MBau,
Welcome to the community! 🙂
Kindly post a .img or .png image of your detailed network diagram as well as the settings you have configured on both SRX5308.
What is the current firmware version of both SRX5308?
Regards,
DaneA
NETGEAR Community Team
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: SRX5308 Only two IPSEC Channels working over same IKE
Hello DaneA,
thank you for your fast reply.
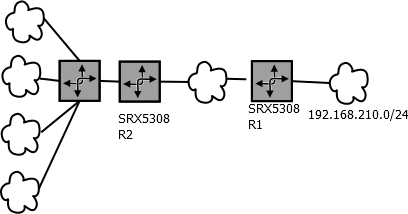
Here´s a simplified image. Through one IKE Tunnel should routed three IPSec Tunnels with different subnets.
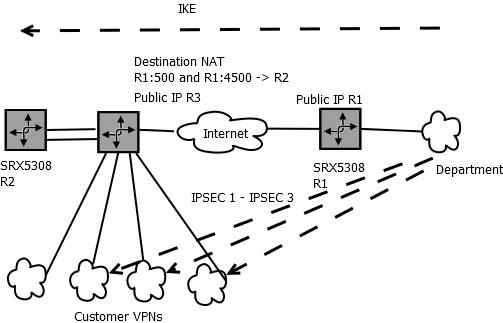
Following the full detailed image to show the real wireing.
Most routers don´t (or didn´t) support routing from vpn to vpn. And if they do, debugging is nearly not possible. So our department build up a IKE Connections to a separeted Router behind the main router realized with destination NAT (Portforwarding on matching source IP). Now it is possible to route to customer VPNs usinge a transfer network.
It works! But only with two of three IPSEC Tunnels. With two random tunnels! Sometimes tunnel one and two. Sometime tunnel two and three.
Best regards
P.S: Firmware: 4.3.4-2
IKE: Preshared Key - Aggressive - AES256 - SHA1 - DH5 - 28800s Lifetime - DPD on
IPSEC: AES256 - SHA1 - DH5 - 3600s
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: SRX5308 Only two IPSEC Channels working over same IKE
I have inquired your concern to a higher tier of NETGEAR Support. On the SRX5308, 125 IPSec VPN policies can run concurrently using the same IKE policy, but the remote endpoint should be same for all IPSec VPN policies using the same IKE policy.
Kindly check that all remote endpoint are the same for all IPSec VPN policies. Also, when one of the policies does not connect, kindly provide the VPN logs relating to this policy to be reviewed.
Regards,
DaneA
NETGEAR Community Team
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: SRX5308 Only two IPSEC Channels working over same IKE
Hi MBau,
We’d greatly appreciate hearing your feedback letting us know if the information we provided has helped resolve your issue or if you need further assistance.
If your issue is now resolved we encourage you to mark the appropriate reply as the “Accepted Solution” so others can be confident in benefiting from the solution. The Netgear community looks forward to hearing from you and being a helpful resource in the future!
Thanks,
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: SRX5308 Only two IPSEC Channels working over same IKE
I`m sorry for the late answer. I was a longer time out of office.
Good to hear that more than two VPN policies can run concurrently using the same IKE policy.
All remote endpoints are the same for all IPSec VPN polices. On the initiater SRX are the official IP used. On responder side are the FQDN used that provide the destination NAT.
Please remeber. It´s random which ipsec connect and which ipsec failed. On next test it may be reverse.
Logs
Pseudonymizations:
Official IP Resonder: 90.90.90.90
Official IP Router with configured Destination NAT: 82.82.82.82
FQDN Router with configured Destination NAT: initiator.domain.com
IKE-Name: Common-IKE
IPSEC Name succeed in this logs: IPSEC-success
IPSEC Name failed in this logs: IPSEC-no-success
Network between Initator SRX and Router with Destination NAT: 192.168.81.0/28
Target Network previous connected (3rd IPSEC) 192.168.200.0/24
Target Network suceed in this log. 172.16.0.0/12
Target Network failed in this log. 10.157.0.0/16
Common Network on Responder side: 192.168.210.0/24
---- Initiator Log ---
Fri Feb 17 10:02:31 2017 (GMT +0000): [SRX5308] [IKE] INFO: IPsec-SA established[UDP encap 4500->4500]: ESP/Tunnel 192.168.81.2->90.90.90.90 with spi=102660786(0x61e7ab2)
Fri Feb 17 10:02:31 2017 (GMT +0000): [SRX5308] [IKE] INFO: IPsec-SA established[UDP encap 4500->4500]: ESP/Tunnel 90.90.90.90->192.168.81.2 with spi=177808823(0xa9925b7)
Fri Feb 17 10:02:30 2017 (GMT +0000): [SRX5308] [IKE] INFO: Adjusting peer's encmode 3(3)->Tunnel(1)
Fri Feb 17 10:02:30 2017 (GMT +0000): [SRX5308] [IKE] INFO: Adjusting encryption mode to use UDP encapsulation
Fri Feb 17 10:02:30 2017 (GMT +0000): [SRX5308] [IKE] INFO: Initiating new phase 2 negotiation: 192.168.81.2[500]<=>90.90.90.90[0]
Fri Feb 17 10:02:30 2017 (GMT +0000): [SRX5308] [IKE] INFO: Configuration found for 90.90.90.90.
Fri Feb 17 10:02:30 2017 (GMT +0000): [SRX5308] [IKE] INFO: Configuration found for 90.90.90.90.
Fri Feb 17 10:02:28 2017 (GMT +0000): [SRX5308] [IKE] INFO: IPsec-SA established[UDP encap 4500->4500]: ESP/Tunnel 192.168.81.2->90.90.90.90 with spi=133915016(0x7fb6188)
Fri Feb 17 10:02:28 2017 (GMT +0000): [SRX5308] [IKE] INFO: IPsec-SA established[UDP encap 4500->4500]: ESP/Tunnel 90.90.90.90->192.168.81.2 with spi=4913542(0x4af986)
Fri Feb 17 10:02:28 2017 (GMT +0000): [SRX5308] [IKE] INFO: Adjusting peer's encmode 3(3)->Tunnel(1)
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: Adjusting encryption mode to use UDP encapsulation
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: Initiating new phase 2 negotiation: 192.168.81.2[0]<=>90.90.90.90[0]
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: Sending Informational Exchange: notify payload[INITIAL-CONTACT]
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: ISAKMP-SA established for 192.168.81.2[4500]-90.90.90.90[4500] with spi:31b493bbd60db694:a128355243714e1d
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: for debugging :: changing portsFri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: port changed !!
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: NAT detected: ME
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: For 90.90.90.90[500], Selected NAT-T version: RFC 3947
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: NAT-D payload matches for 90.90.90.90[500]
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: NAT-D payload does not match for 192.168.81.2[500]
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: Received Vendor ID: DPD
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: Received Vendor ID: RFC 3947
Fri Feb 17 10:02:27 2017 (GMT +0000): [SRX5308] [IKE] INFO: Received Vendor ID: KAME/racoon
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: [isakmp_agg.c:261]: XXX: setting vendorid: 9
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: [isakmp_agg.c:261]: XXX: setting vendorid: 8
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: [isakmp_agg.c:261]: XXX: setting vendorid: 4
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: [isakmp_agg.c:257]: XXX: NUMNATTVENDORIDS: 3
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: NAT-Traversal is Enabled
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: Beginning Aggressive mode.
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: Initiating new phase 1 negotiation: 192.168.81.2[500]<=>90.90.90.90[500]
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: Configuration found for 90.90.90.90.
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: Configuration found for 90.90.90.90.
Fri Feb 17 10:02:26 2017 (GMT +0000): [SRX5308] [IKE] INFO: Using IPsec SA configuration: 192.168.200.0/24<->192.168.210.0/24
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] INFO: accept a request to establish IKE-SA: 90.90.90.90
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] INFO: Adding IKE configuration with identifier "Common-IKE"
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] INFO: Adding IPSec configuration with identifier "IPSEC-success"
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] INFO: IKE configuration with identifier "Common-IKE" deleted sucessfully
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] WARNING: no phase1 found for "Common-IKE"
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] ERROR: Failed to Delete the IPSec configuration with identifier "IPSEC-success"
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] ERROR: sainfo identifier not found ("IPSEC-success")
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] ERROR: No policy found: 192.168.210.0/24[0] 172.16.0.0/12[0] proto=any dir=in
Fri Feb 17 10:02:25 2017 (GMT +0000): [SRX5308] [IKE] ERROR: No policy found: 172.16.0.0/12[0] 192.168.210.0/24[0] proto=any dir=out
Fri Feb 17 10:02:24 2017 (GMT +0000): [SRX5308] [IKE] INFO: accept a request to establish IKE-SA: 90.90.90.90
Fri Feb 17 10:02:24 2017 (GMT +0000): [SRX5308] [IKE] INFO: Adding IKE configuration with identifier "Common-IKE"
Fri Feb 17 10:02:24 2017 (GMT +0000): [SRX5308] [IKE] INFO: Adding IPSec configuration with identifier "IPSEC-no-success"
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: IKE configuration with identifier "Common-IKE" deleted sucessfully
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: an undead schedule has been deleted: 'purge_remote'.
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: Purged ISAKMP-SA with spi=027be29244ab4279:2a4d9b3466d1544a.
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: [IPSEC_VPN] Purged IPsec-SA with spi=128843844(0x7ae0044).
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: [IPSEC_VPN] Purged IPsec-SA with spi=96370306(0x5be7e82).
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: [IPSEC_VPN] Purged IPsec-SA with spi=107054870(0x6618716).
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: [IPSEC_VPN] Purged IPsec-SA with spi=10625958(0xa223a6).
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: [IPSEC_VPN] Purged IPsec-SA with spi=186861013(0xb2345d5).
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: an undead schedule has been deleted: 'pk_recvupdate'.
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] INFO: Sending Informational Exchange: delete payload[]
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] WARNING: no phase2 bounded.
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] ERROR: Failed to Delete the IPSec configuration with identifier "IPSEC-no-success"
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] ERROR: sainfo identifier not found ("IPSEC-no-success")
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] ERROR: No policy found: 192.168.210.0/24[0] 10.157.0.0/16[0] proto=any dir=in
Fri Feb 17 10:02:23 2017 (GMT +0000): [SRX5308] [IKE] ERROR: No policy found: 10.157.0.0/16[0] 192.168.210.0/24[0] proto=any dir=out
--- Responder Log ---
Fri Feb 17 11:02:31 2017 (GMT +0100): [SRX5308] [IKE] INFO: IPsec-SA established[UDP encap 4500->26334]: ESP/Tunnel 90.90.90.90->82.82.82.82 with spi=177808823(0xa9925b7)
Fri Feb 17 11:02:31 2017 (GMT +0100): [SRX5308] [IKE] INFO: IPsec-SA established[UDP encap 26334->4500]: ESP/Tunnel 82.82.82.82->90.90.90.90 with spi=102660786(0x61e7ab2)
Fri Feb 17 11:02:31 2017 (GMT +0100): [SRX5308] [IKE] INFO: Ignoring request for negotiation to 82.82.82.82 as Local is configured as Responder.
Fri Feb 17 11:02:31 2017 (GMT +0100): [SRX5308] [IKE] INFO: remote configuration for identifier "initator.domain.com" found
Fri Feb 17 11:02:31 2017 (GMT +0100): [SRX5308] [IKE] INFO: remote configuration for identifier "initator.domain.com" found
Fri Feb 17 11:02:31 2017 (GMT +0100): [SRX5308] [IKE] INFO: Using IPsec SA configuration: 192.168.210.0/24<->10.157.0.0/16
Fri Feb 17 11:02:30 2017 (GMT +0100): [SRX5308] [IKE] INFO: Adjusting peer's encmode 3(3)->Tunnel(1)
Fri Feb 17 11:02:30 2017 (GMT +0100): [SRX5308] [IKE] INFO: Using IPsec SA configuration: 192.168.210.0/24<->172.16.0.0/12
Fri Feb 17 11:02:30 2017 (GMT +0100): [SRX5308] [IKE] INFO: Responding to new phase 2 negotiation: 90.90.90.90[0]<=>82.82.82.82[0]
Fri Feb 17 11:02:29 2017 (GMT +0100): [SRX5308] [IKE] INFO: an undead schedule has been deleted: 'pk_recvupdate'.
Fri Feb 17 11:02:29 2017 (GMT +0100): [SRX5308] [IKE] INFO: Sending Informational Exchange: delete payload[]
Fri Feb 17 11:02:28 2017 (GMT +0100): [SRX5308] [IKE] INFO: IPsec-SA established[UDP encap 4500->26334]: ESP/Tunnel 90.90.90.90->82.82.82.82 with spi=4913542(0x4af986)
Fri Feb 17 11:02:28 2017 (GMT +0100): [SRX5308] [IKE] INFO: IPsec-SA established[UDP encap 26334->4500]: ESP/Tunnel 82.82.82.82->90.90.90.90 with spi=133915016(0x7fb6188)
Fri Feb 17 11:02:28 2017 (GMT +0100): [SRX5308] [IKE] INFO: Adjusting peer's encmode 3(3)->Tunnel(1)
Fri Feb 17 11:02:28 2017 (GMT +0100): [SRX5308] [IKE] INFO: Using IPsec SA configuration: 192.168.210.0/24<->192.168.200.0/24
Fri Feb 17 11:02:28 2017 (GMT +0100): [SRX5308] [IKE] INFO: Responding to new phase 2 negotiation: 90.90.90.90[0]<=>82.82.82.82[0]
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Sending Informational Exchange: notify payload[INITIAL-CONTACT]
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: ISAKMP-SA established for 90.90.90.90[4500]-82.82.82.82[26334] with spi:31b493bbd60db694:a128355243714e1d
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: NAT detected: Peer is behind a NAT device
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: NAT-D payload does not match for 82.82.82.82[26334]
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: NAT-D payload matches for 90.90.90.90[4500]
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Floating ports for NAT-T with peer 82.82.82.82[26334]
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Ignoring request for negotiation to 82.82.82.82 as Local is configured as Responder.
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: remote configuration for identifier "initator.domain.com" found
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: remote configuration for identifier "initator.domain.com" found
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: For 82.82.82.82[9062], Selected NAT-T version: RFC 3947Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Using IPsec SA configuration: 192.168.210.0/24<->172.16.0.0/12
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Received Vendor ID: DPD
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Received Vendor ID: RFC 3947
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Received Vendor ID: draft-ietf-ipsec-nat-t-ike-02
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Received Vendor ID: RFC XXXX
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Beginning Aggressive mode.
Fri Feb 17 11:02:27 2017 (GMT +0100): [SRX5308] [IKE] INFO: Received request for new phase 1 negotiation: 90.90.90.90[500]<=>82.82.82.82[9062]
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Re: SRX5308 Only two IPSEC Channels working over same IKE
Another little thing.
After then i tryed to connect the failed VPN with "IPSEC Connection Status" -> "Connect Button"
Log
Fri Feb 17 11:43:13 2017 (GMT +0100): [SRX5308] [IKE] WARNING: scheduler is already scheduled for SA creation for remote: "90.90.90.90"
Fri Feb 17 11:43:13 2017 (GMT +0100): [SRX5308] [IKE] ERROR: Failed to attach schedSaCreate in IKE configuraion
Fri Feb 17 11:43:13 2017 (GMT +0100): [SRX5308] [IKE] INFO: accept a request to establish IKE-SA: 90.90.90.90